Exposure of sensitive Information allows account takeover
June 9, 2025

Products Impacted
This vulnerability is present in all versions of BackendAI. We tested on version 25.3.3 (commit f7f8fe33ea0230090f1d0e5a936ef8edd8cf9959).
CVSS Score: 8.0
AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H
CWE Categorization
CWE-200: Exposure of Sensitive Information
Details
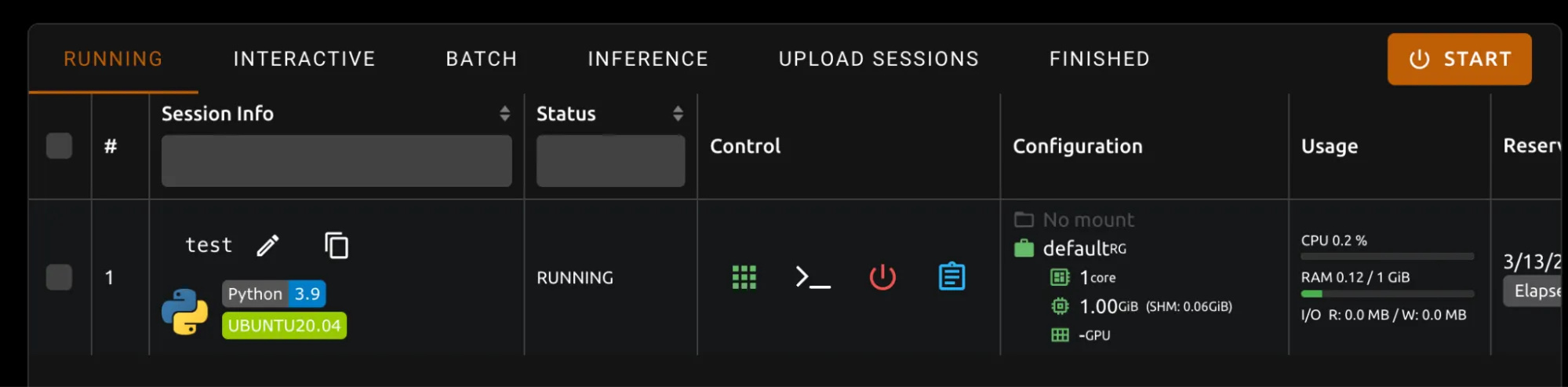
To reproduce this, we started an interactive session
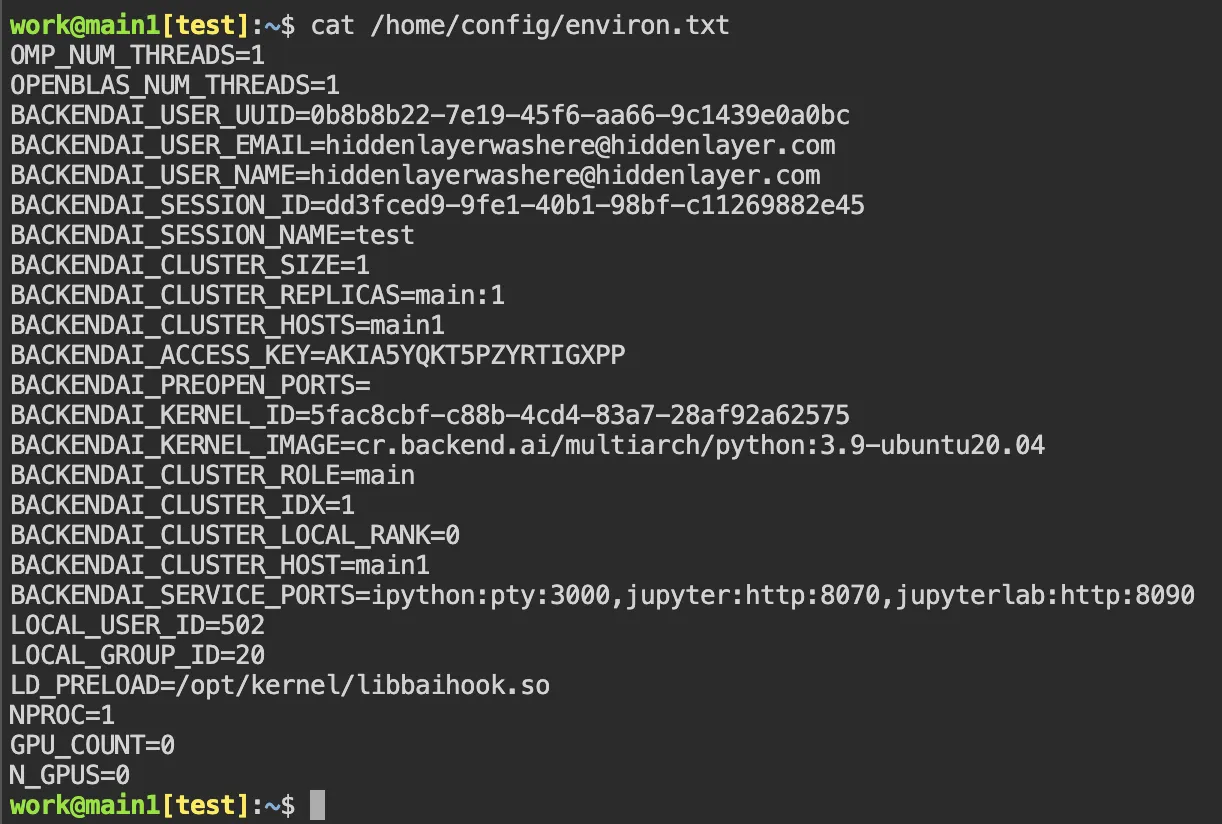
Then, we can read /home/config/environ.txt and read the information.
Timeline
March 28, 2025 — Contacted vendor to let them know we have identified security vulnerabilities and ask how we should report them.
April 02, 2025 — Vendor answered letting us know their process, which we followed to send the report.
April 21, 2025 — Vendor sent confirmation that their security team was working on actions for two of the vulnerabilities and they were unable to reproduce another.
April 21, 2025 — Follow up email sent providing additional steps on how to reproduce the third vulnerability and offered to have a call with them regarding this.
May 30, 2025 — Attempt to reach out to vendor prior to public disclosure date.
June 03, 2025 — Final attempt to reach out to vendor prior to public disclosure date.
June 09, 2025 — HiddenLayer public disclosure.
Project URL
https://github.com/lablup/backend.ai
Researcher: Esteban Tonglet, Security Researcher, HiddenLayer
Researcher: Kasimir Schulz, Director, Security Research, HiddenLayer
Related SAI Security Advisory
February 26, 2026
Flair Vulnerability Report
An arbitrary code execution vulnerability exists in the LanguageModel class due to unsafe deserialization in the load_language_model method. Specifically, the method invokes torch.load() with the weights_only parameter set to False, which causes PyTorch to rely on Python’s pickle module for object deserialization.
November 26, 2025
Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
When in autorun mode, Cursor checks commands sent to run in the terminal to see if a command has been specifically allowed. The function that checks the command has a bypass to its logic allowing an attacker to craft a command that will execute non-allowed commands.