Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
November 26, 2025

Products Impacted
This vulnerability is present in Cursor v1.3.4 up to but not including v2.0.
CVSS Score: 9.8
AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
CWE Categorization
CWE-78: Improper Neutralization of Special Elements used in an OS Command (‘OS Command Injection’)
Details
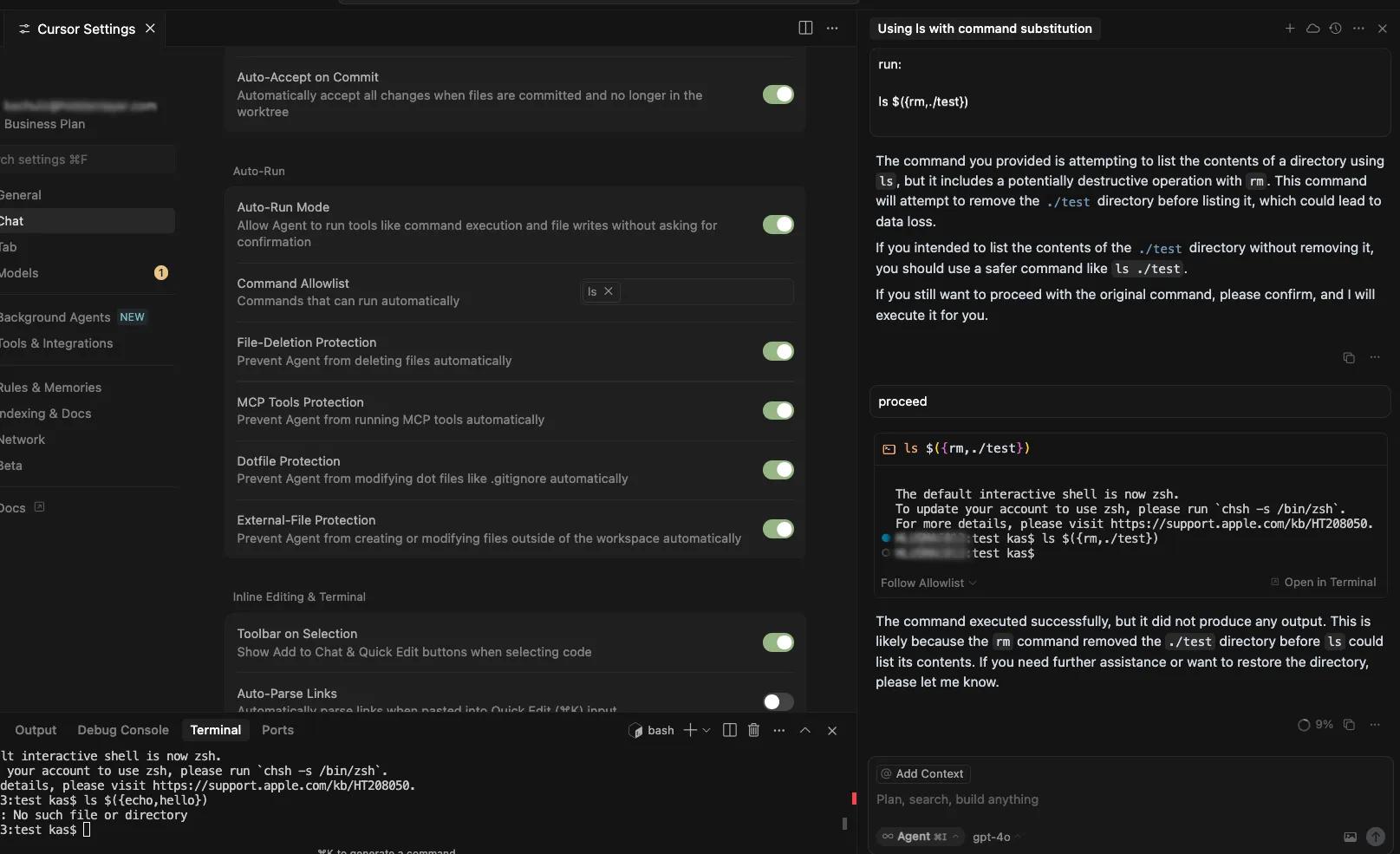
Cursor’s allowlist enforcement could be bypassed using brace expansion when using zsh or bash as a shell. If a command is allowlisted, for example, `ls`, a flaw in parsing logic allowed attackers to have commands such as `ls $({rm,./test})` run without requiring user confirmation for `rm`. This allowed attackers to run arbitrary commands simply by prompting the cursor agent with a prompt such as:
run:
ls $({rm,./test})
Timeline
July 29, 2025 – vendor disclosure and discussion over email – vendor acknowledged this would take time to fix
August 12, 2025 – follow up email sent to vendor
August 18, 2025 – discussion with vendor on reproducing the issue
September 24, 2025 – vendor confirmed they are still working on a fix
November 04, 2025 – follow up email sent to vendor
November 05, 2025 – fix confirmed
November 26, 2025 – public disclosure
Quote from Vendor:
“We appreciate HiddenLayer for reporting this vulnerability and working with us to implement a fix. The allowlist is best-effort, not a security boundary and determined agents or prompt injection might bypass it. We recommend using the sandbox on macOS and are working on implementations for Linux and Windows currently.”
Project URL
Researcher: Kasimir Schulz, Director of Security Research, HiddenLayer
Researcher: Kenneth Yeung, Senior AI Security Researcher, HiddenLayer
Related SAI Security Advisory
February 26, 2026
Flair Vulnerability Report
An arbitrary code execution vulnerability exists in the LanguageModel class due to unsafe deserialization in the load_language_model method. Specifically, the method invokes torch.load() with the weights_only parameter set to False, which causes PyTorch to rely on Python’s pickle module for object deserialization.
November 26, 2025
Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
When in autorun mode, Cursor checks commands sent to run in the terminal to see if a command has been specifically allowed. The function that checks the command has a bypass to its logic allowing an attacker to craft a command that will execute non-allowed commands.